Quordle needs to be approached in a different way to Wordle. With four puzzles to solve in nine guesses, you can’t blindly throw letters at it and expect to win – you’ll stand a far better chance if you think strategically.
That’s the case in Wordle too, of course, but it’s even more important in Quordle.
There are two key things to remember.
1. Use several starting words
Firstly, you won’t want just a single starting word, but almost certainly two or three starting words.
The first of these should probably be one of the best Wordle starting words, because the same things that make them work well will apply here too. But after that, you should select another word or possibly two that use up lots more of the most common consonants and that include any remaining vowels.
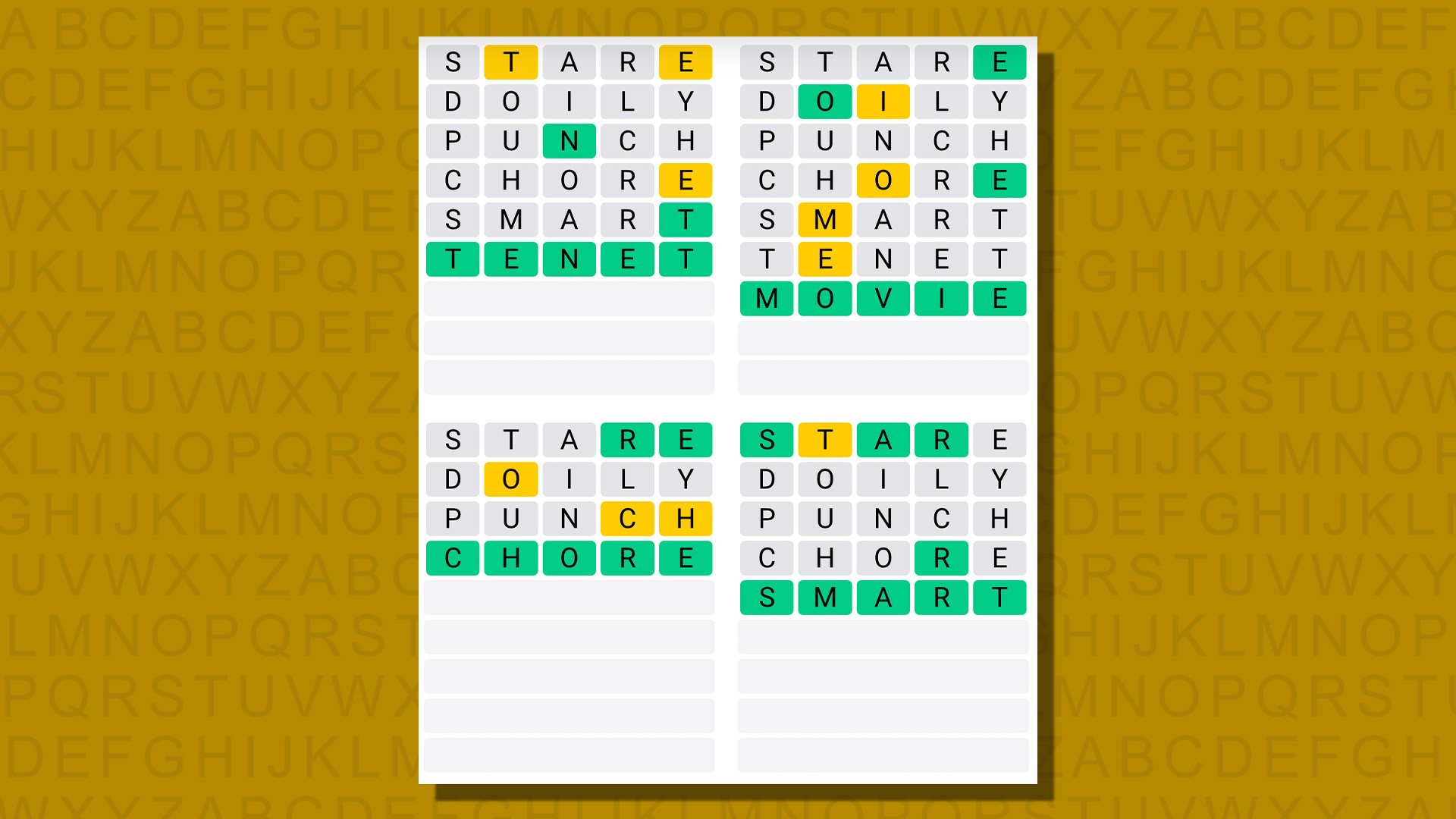
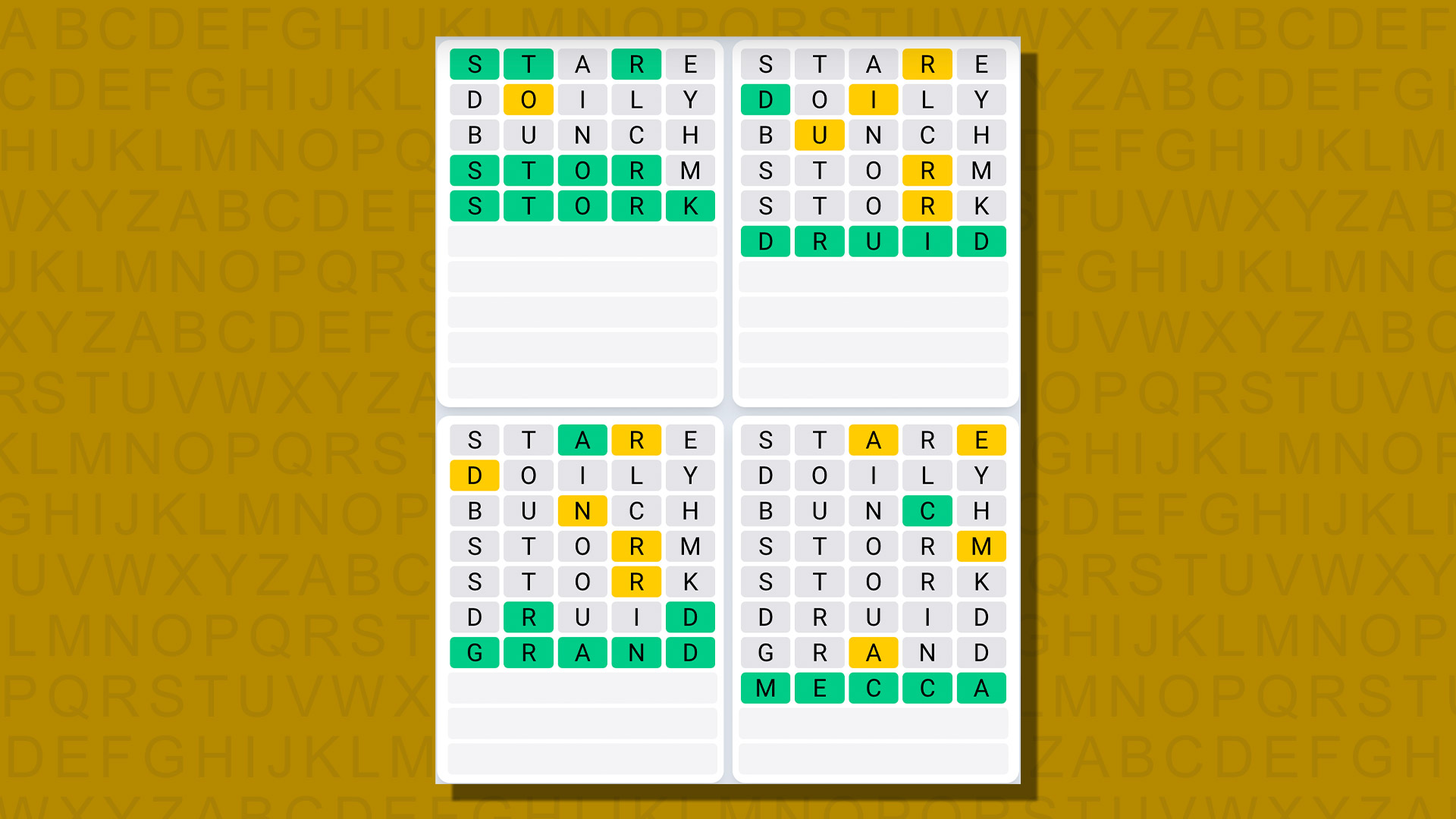
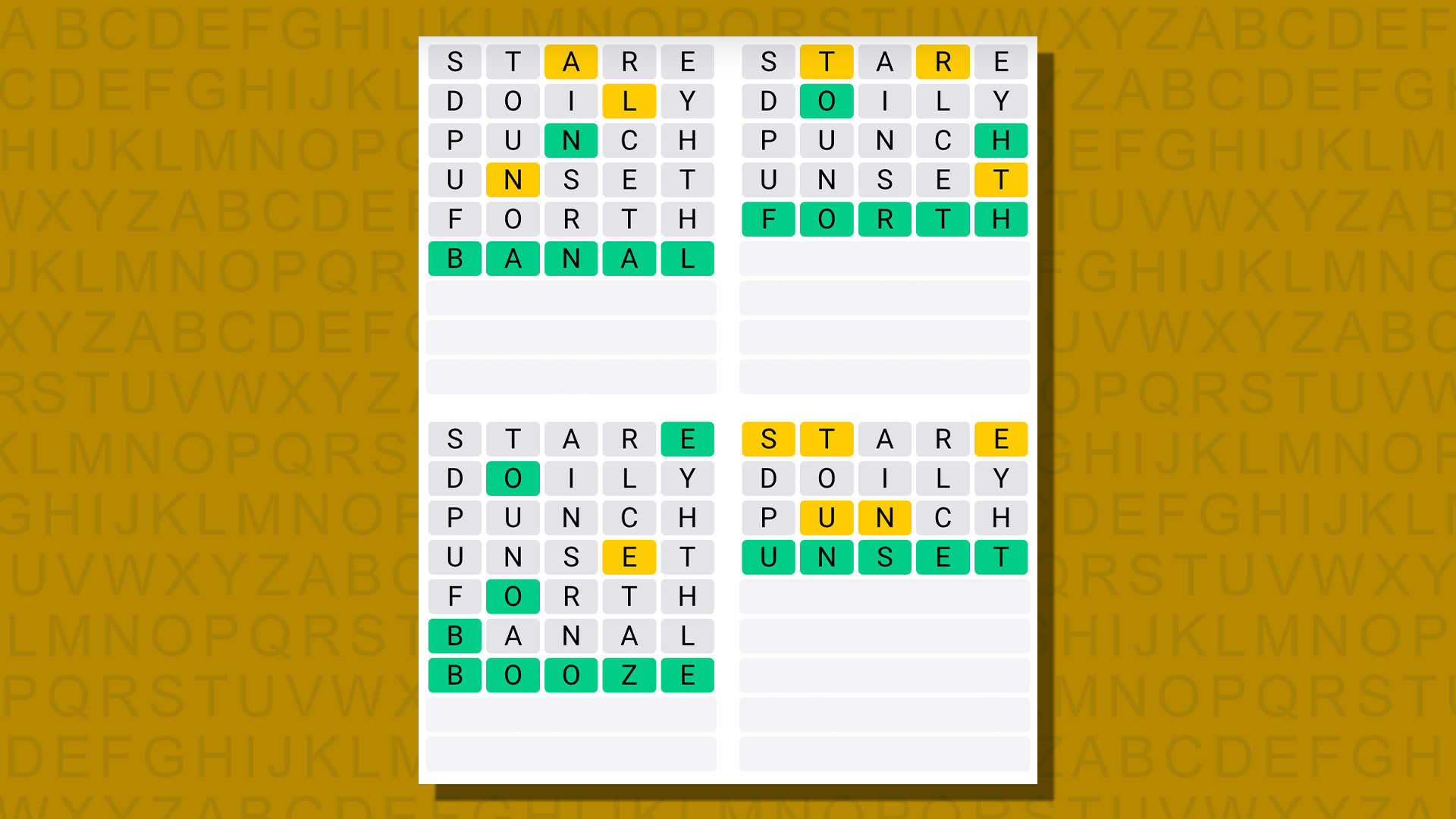
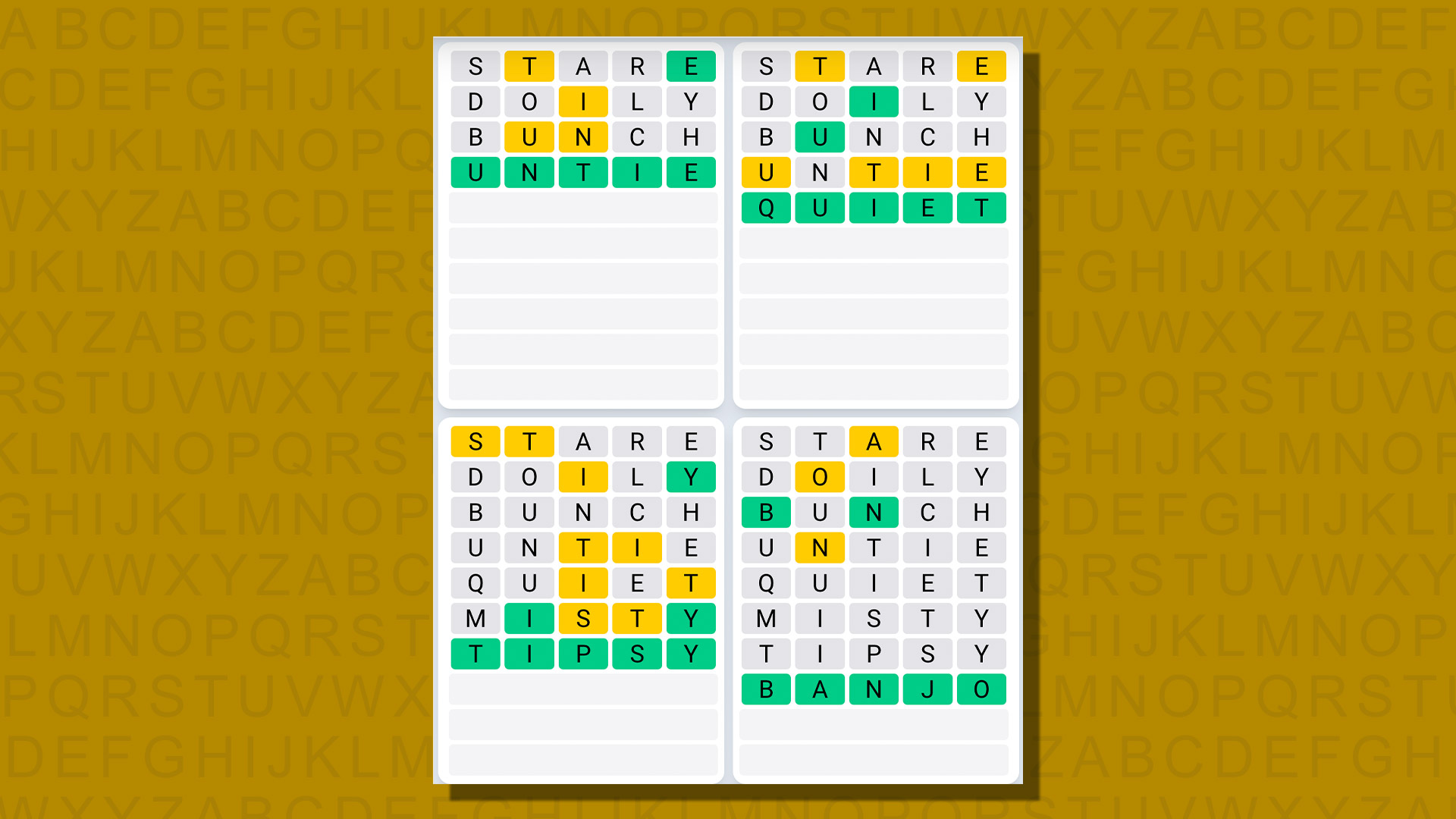
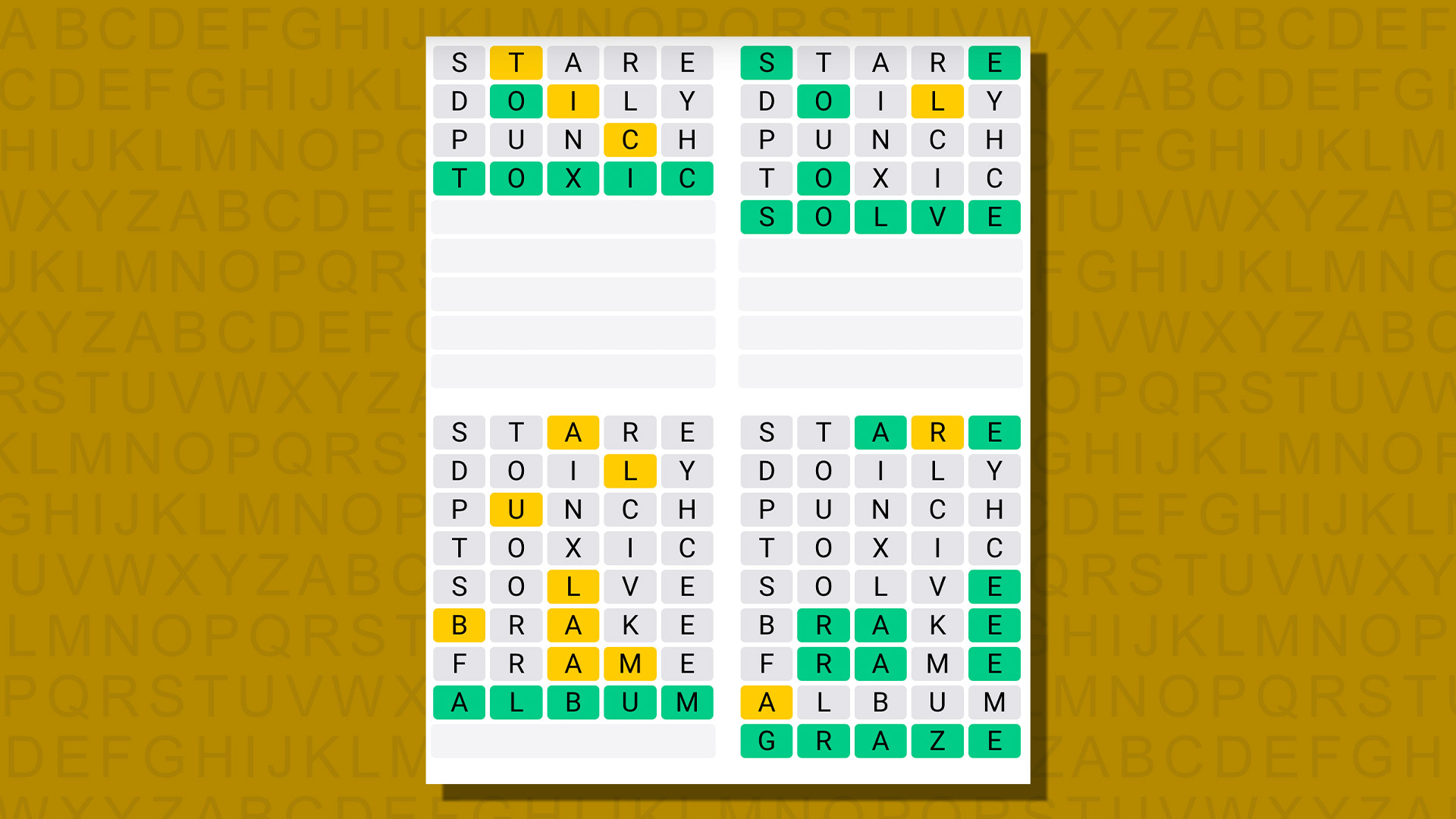
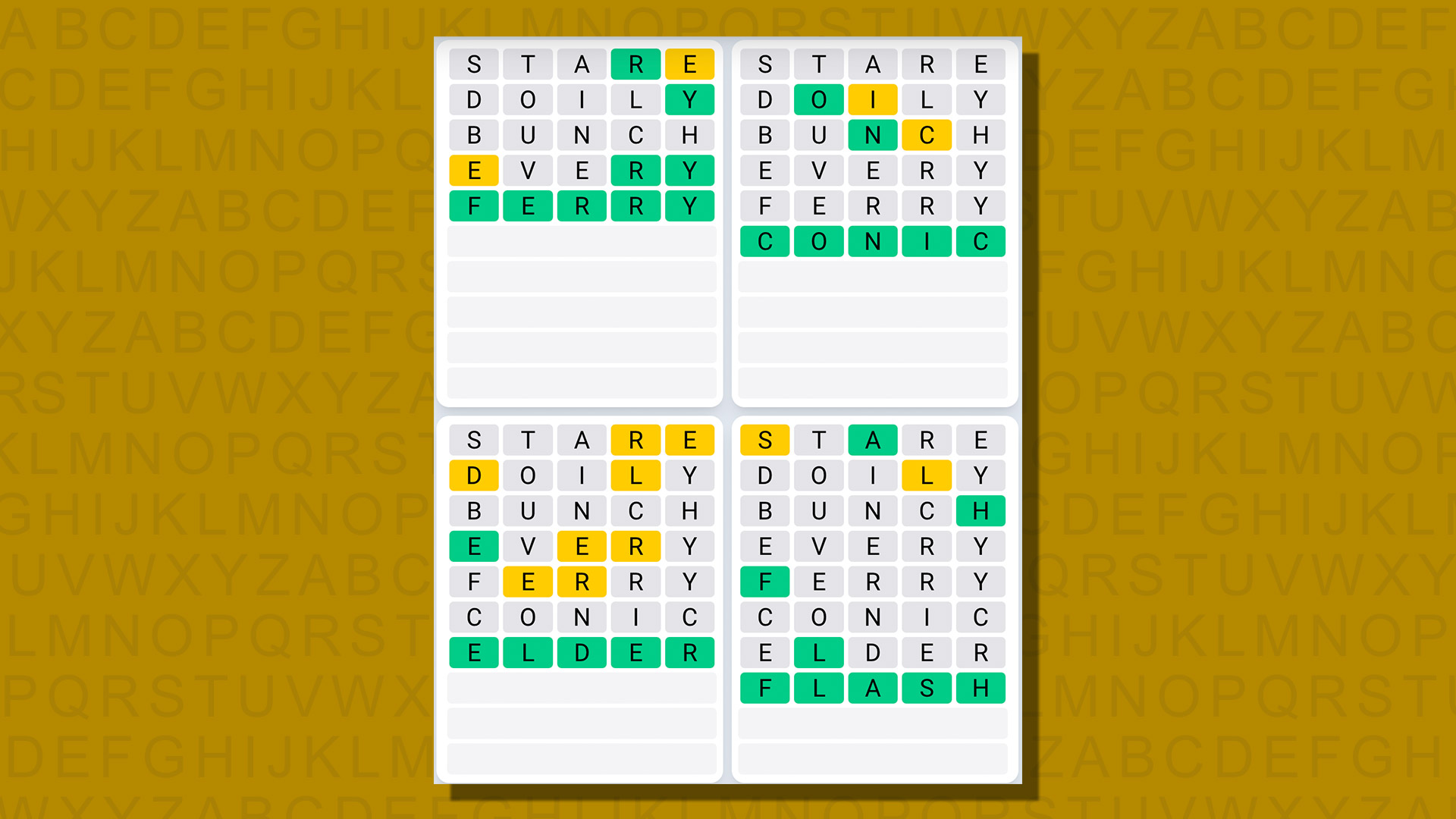
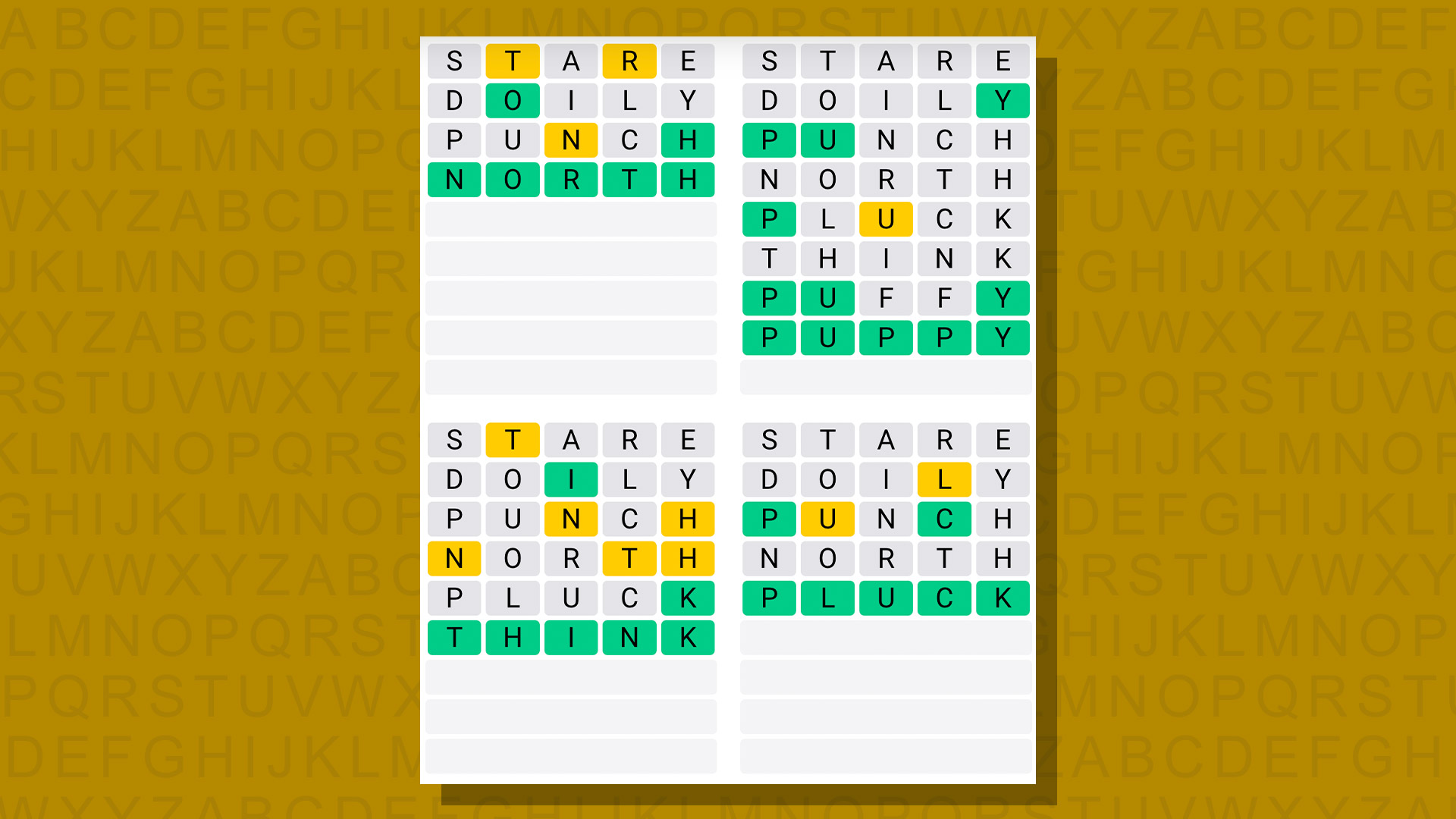
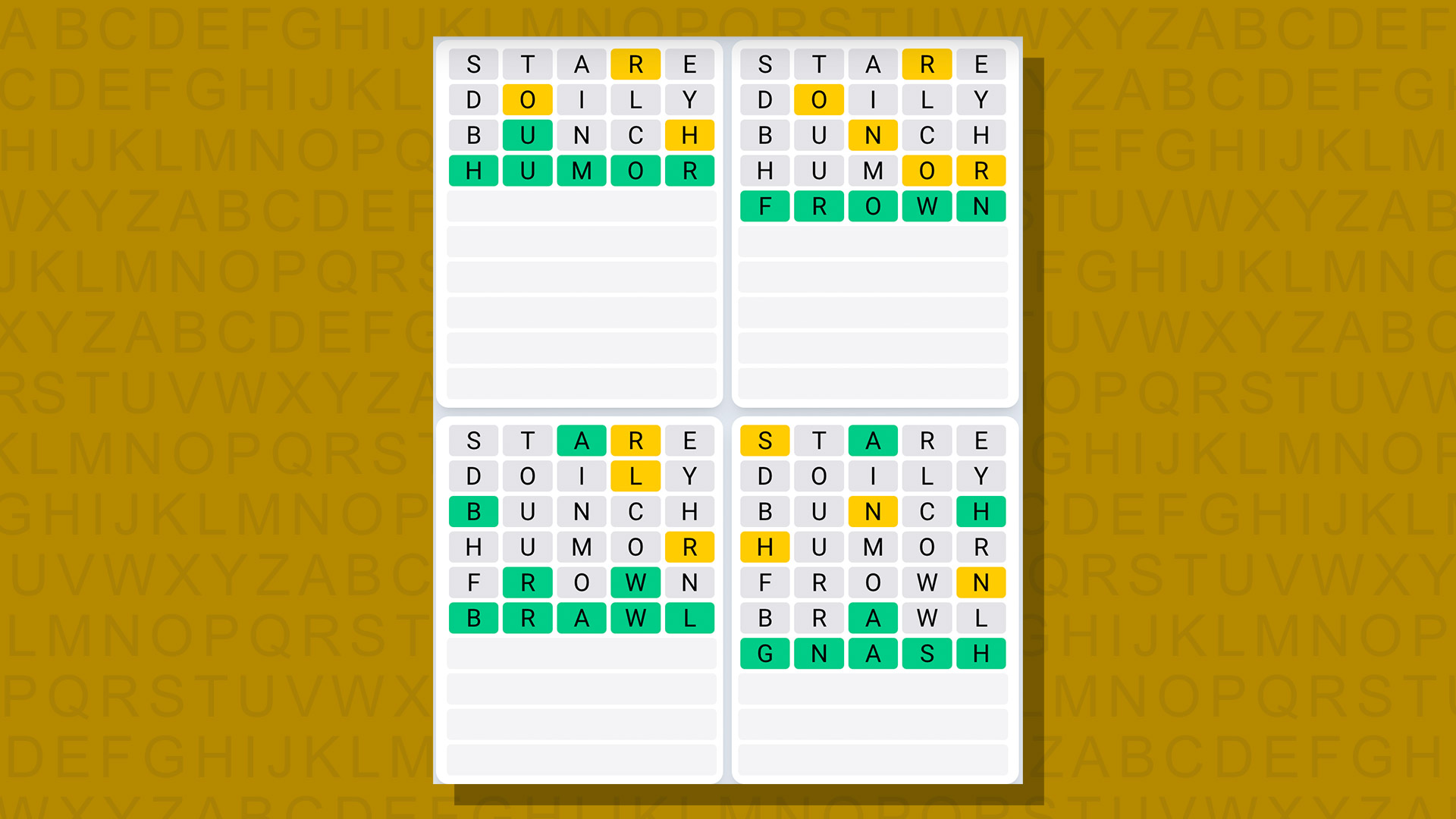
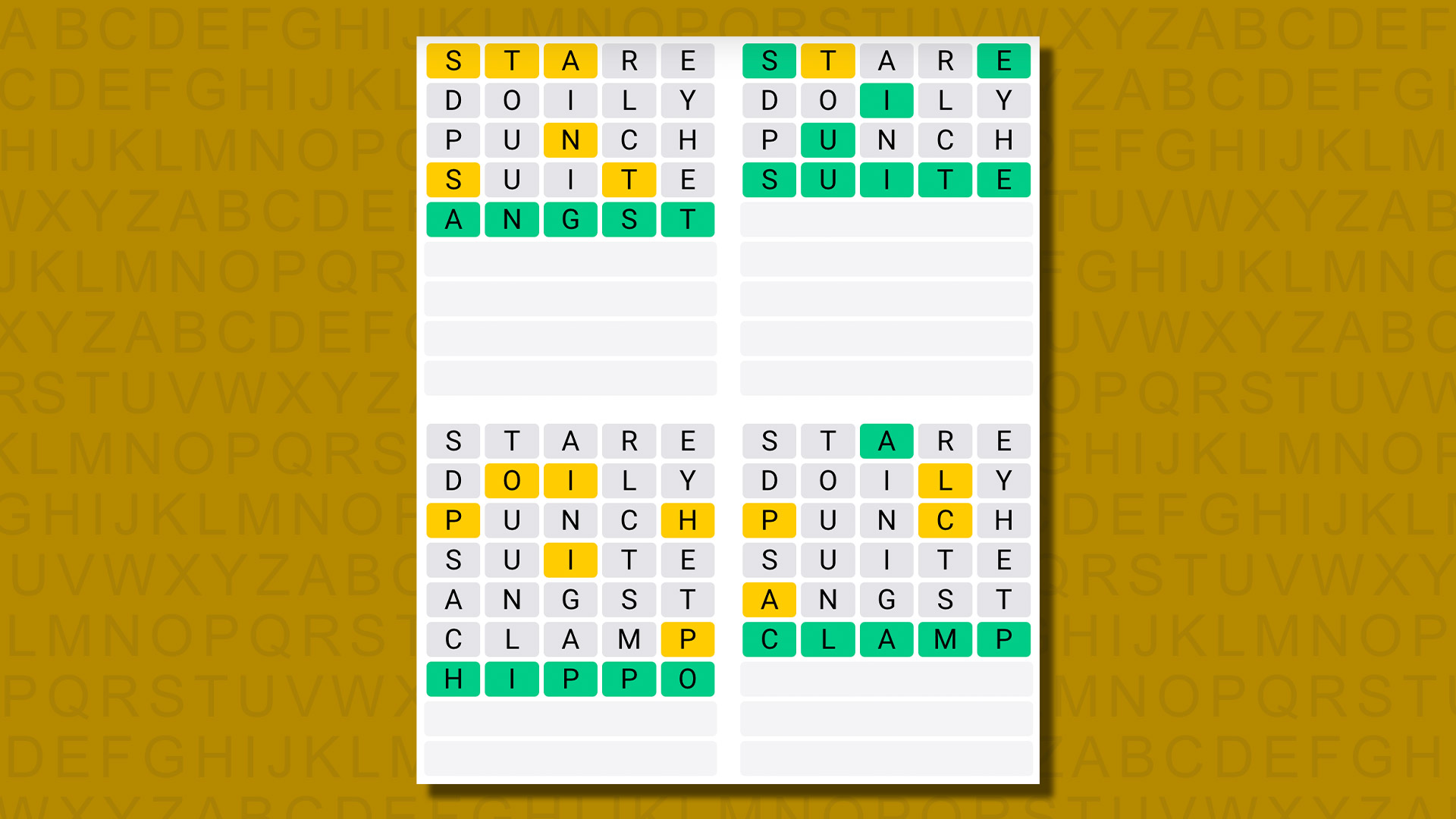
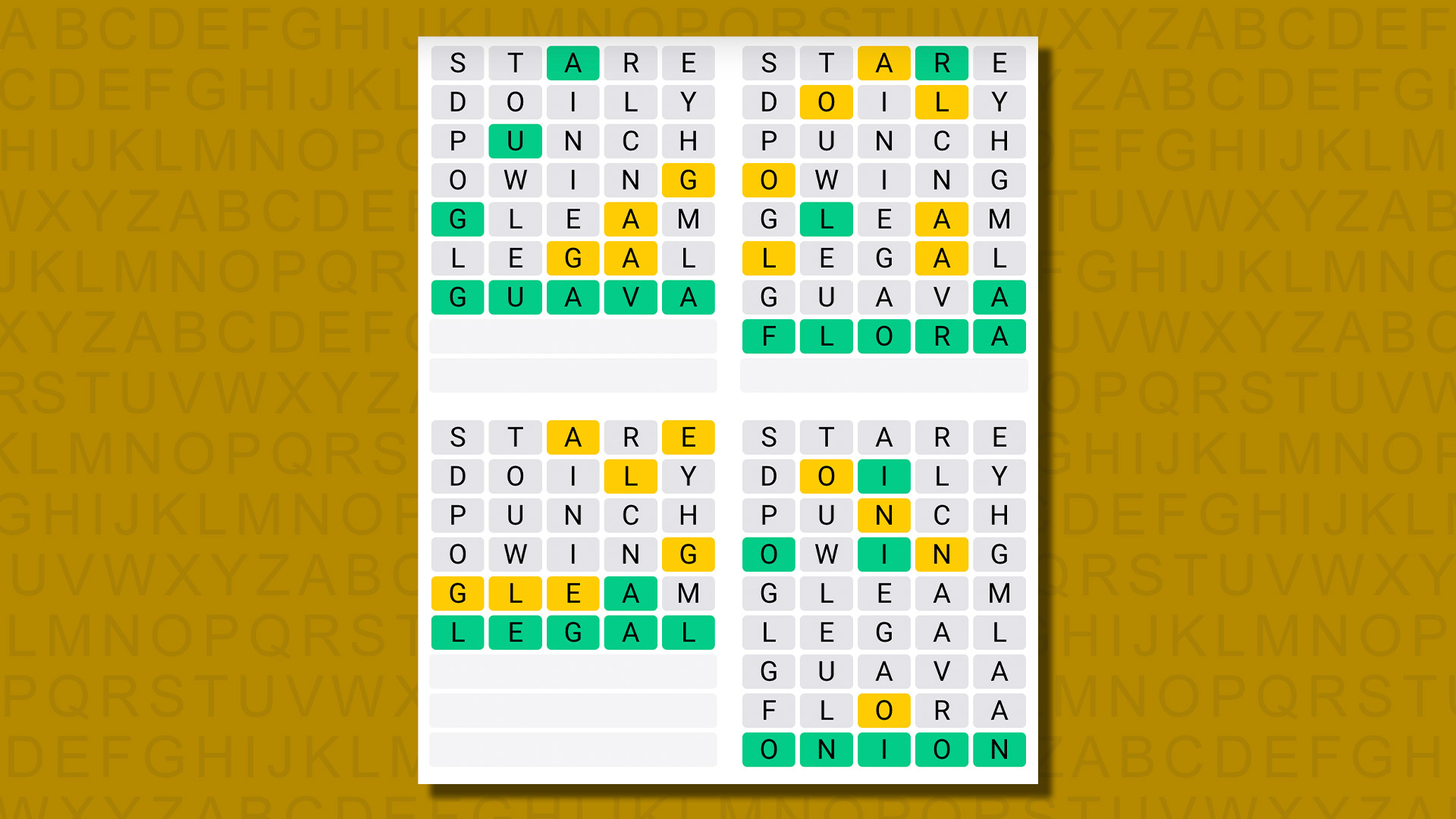
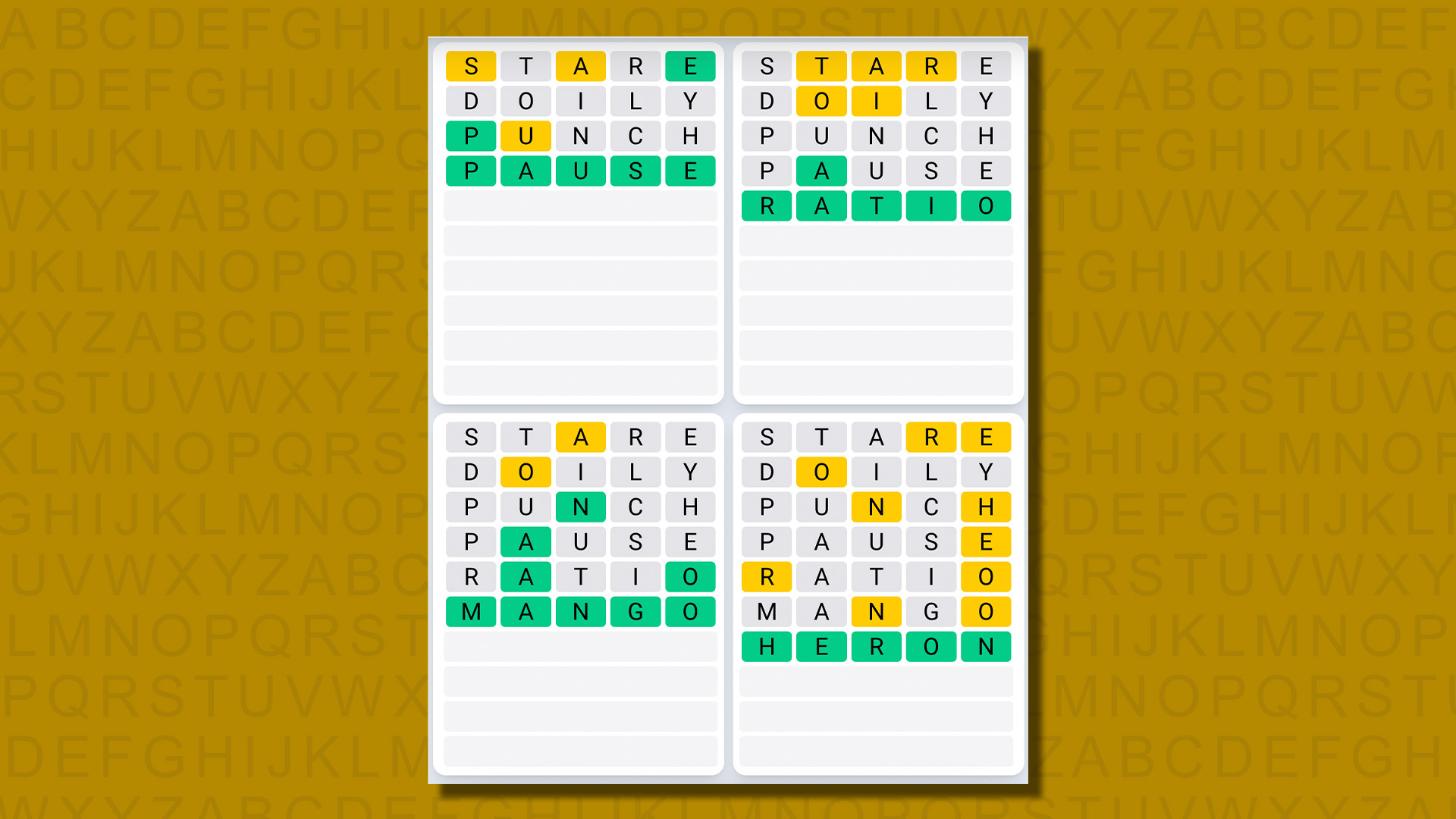
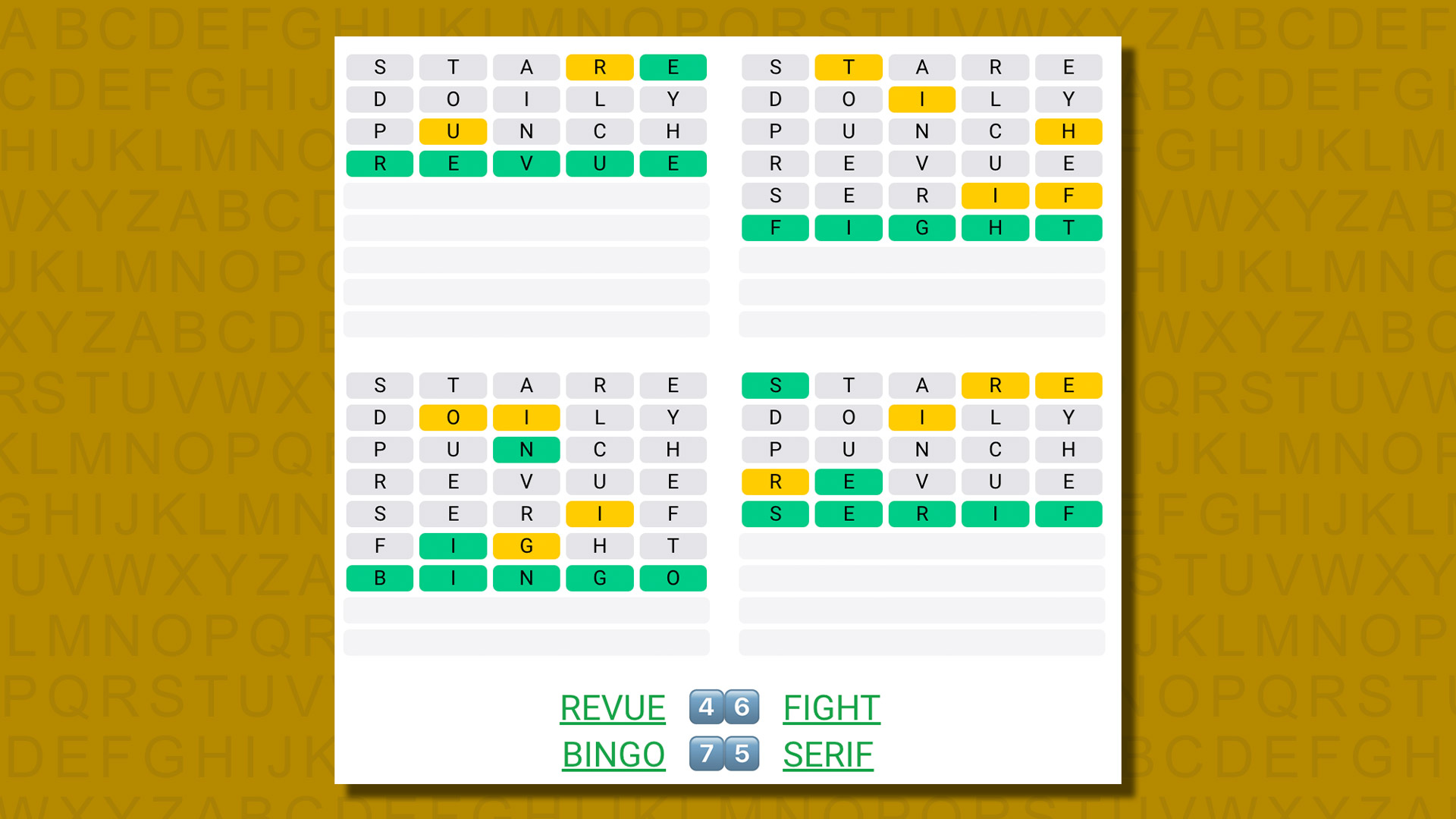
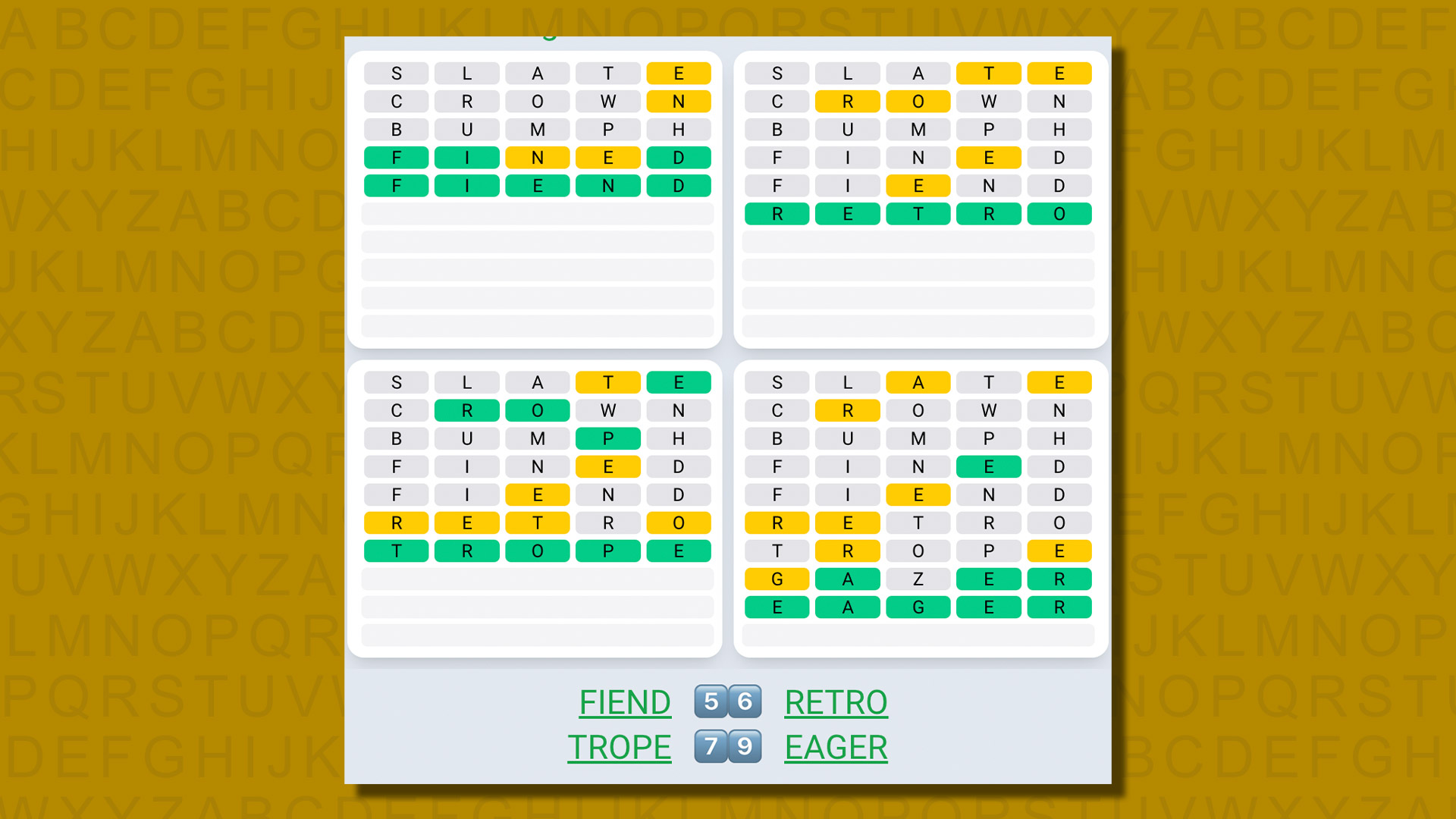
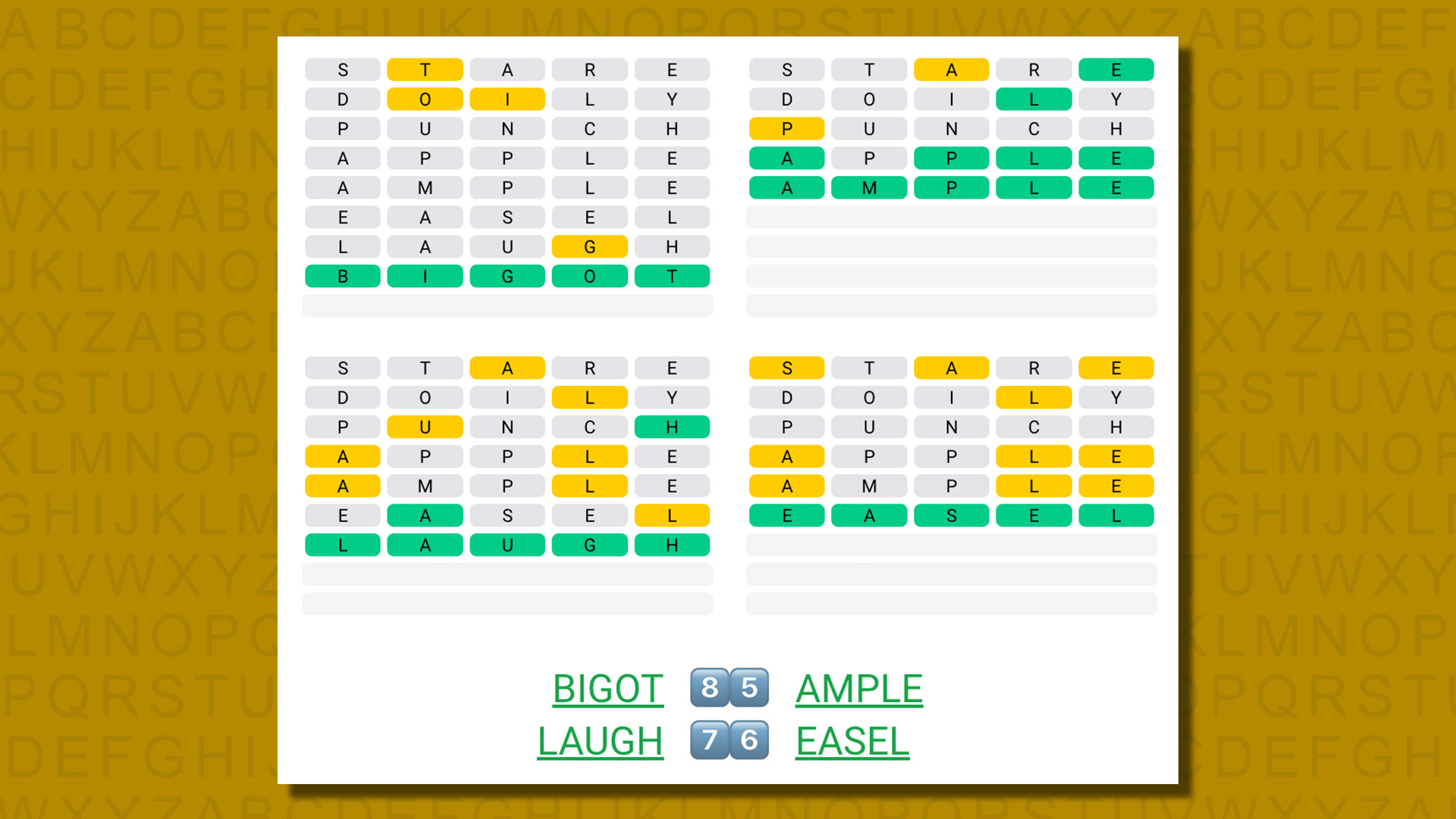
For instance, I currently use STARE > DOILY > PUNCH. Between them, these three words use 15 of the 26 letters in the alphabet including all five vowels, Y, and nine of the most common consonants (S, T, R, D, L, P, N, C and H). There are plenty of other options – you might want to get an M, B, F or G in there instead of the H, maybe – but something like that should do the trick.
If all goes well, that will give you a good lead on what one or sometimes two of the answers might be. If not, well good luck!
2. Narrow things down
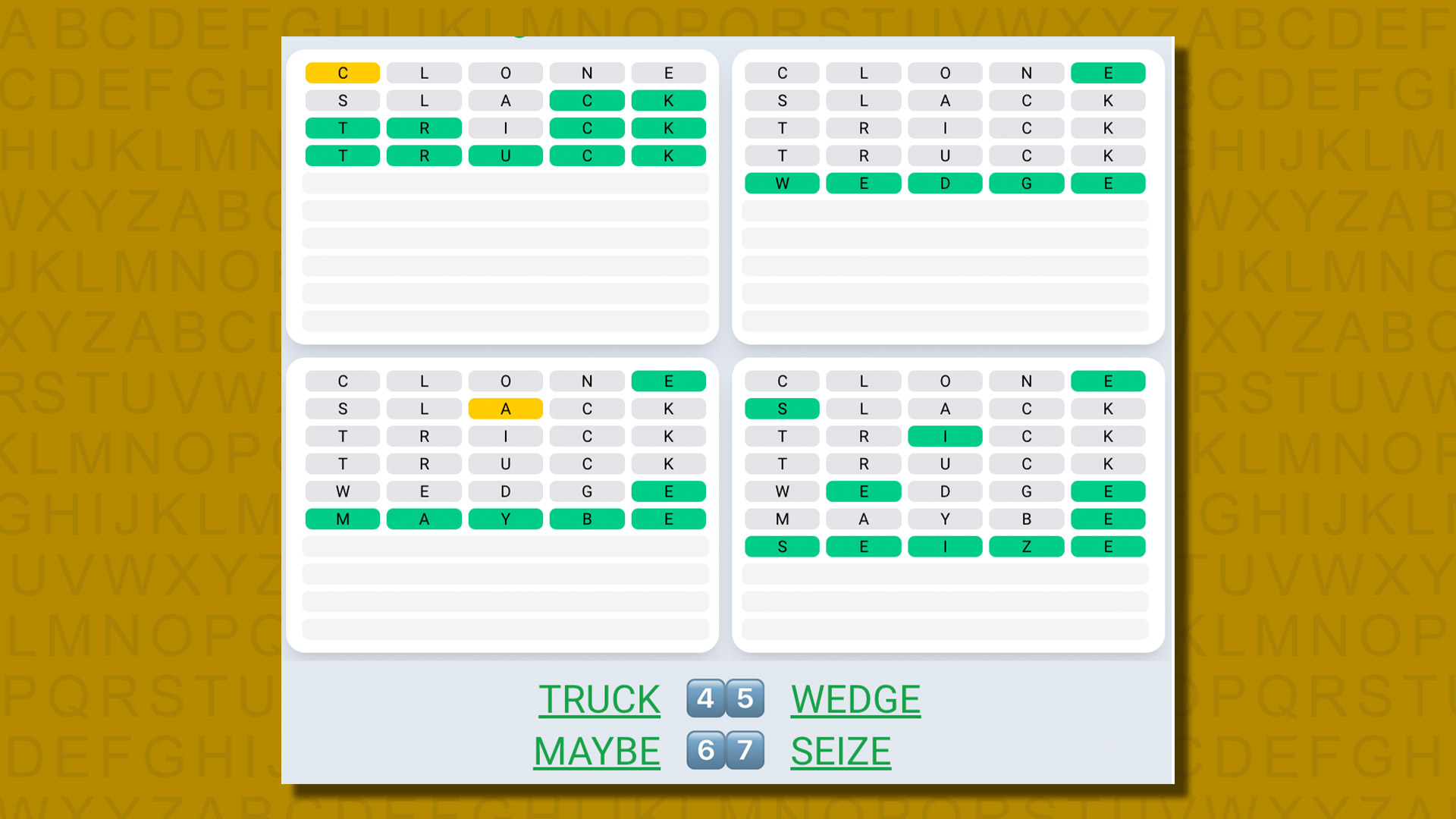
Secondly, if you’re faced with a word where the answer might easily be one of several options – for instance -ATCH, where it could be MATCH, BATCH, LATCH, CATCH, WATCH, HATCH or PATCH – you’ll definitely want to guess a word that would narrow down those options.
In Wordle, you can instead try several of those in succession and hope one is right, assuming you have enough guesses left. It’s risky, but will sometimes work. Plus, it’s the only option in Hard mode. But in Quordle, this will almost certainly result in a failure – you simply don’t have enough guesses.
In the scenario above, CLAMP would be a great guess, as it could point the way to four of the seven words in one go.